Humans
To protect and to digitize
Cybersecurity and the protection of digital environments are becoming more and more crucial today, professional figures such as Carlo are precious for companies and beyond.
Mar 2018
The growing use of digital technologies such as the cloud, big data, mobile, IIoT (Industrial Internet of Things) and artificial intelligence, has led to facing ever larger challenges in terms of data security and protection.
In 2017, 978 million people were victims of a cyber attack and "Cybersecurity" remains among the three most searched words on the most famous portal in the world, Google. This significant increase underscores the importance of all those activities and professions aimed at ensuring the protection of the billions of bits of data and information that are exchanged every day through IT tools by companies, institutions, governments or individuals.
Carlo Porro is the brain of Avio Aero behind the security of one of our most important assets: our intellectual property. Carlo works with the Information Technology Risk and Compliance team at GE Aviation to ensure continuous monitoring, preventive controls and rapid responses to virus infections and other cyber-attacks.
How long have you been a Senior Vulnerability Management Advisor and what are your main responsibilities?
"I began my activity at Avio Aero in 2006, and since the beginning I have taken care of the computer security aspects. Since then, many things have changed; the internet and social media have transformed the points of references. We have moved from passive security to active, preventive security. The advent of social media and big data has shook up the IT scenario and the risks related to it. Since the acquisition by GE, also my role has changed, the centralization of IT systems has moved the security perimeter, but at the same time it has offered me the opportunity to be part of a larger team with many specialized skills."
What was your path before landing in this position, did you work in other industries or are you fond of aeronautics?
"My path towards cybersecurity was gradual, starting with the security management of clients (the machines or networks on which individual users operate, ed.), passing through the security of the company perimeter, finally arriving at handling security at 360 degrees. I have worked in various sectors from Information Technology, to the tertiary sector and telecommunications, but never before has the protection of company data, the protection of our activities, been so important. The information we manage is the basis of the know-how of our company and of our activities and it must be protected in the best way possible."
What is the most stimulating aspect and the main mission for you, when thinking about your work?
"Surely the continuous search for solutions that allow the right balance between the needs of interaction between the company and the outside world, and protection from the outside world. On the Internet there are many people and organizations, criminals or other, interested in collecting, manipulating and reselling personal or business information."
Which GE Aviation teams do you work with the most and what was the main exchange of knowledge with the team overseas?
"Surely my reference group is that of the Cyber Security of GE. With them we exchange a lot of information concerning the tools used, the methods of attack, external threats and defense methodologies. Only through teamwork, of course that carried out alongside colleagues from Avio Aero Lifecycle, Network e Digital Operations teams, is it possible to obtain significant results."
Is there any expert advice that people could use with personal or domestic devices?
"We are now connected to the Internet with different tools, ranging from computers to modern smartphones and tablets. We constantly supply information that concerns us, we post photos, we post comments, we leave tracks on our position, on our purchases, our preferences, our friends and family, at all times. But we are extremely vulnerable. We use technologies that we know very little, created by other people and that present many weaknesses. This combination, with the information we provide and the tools we use, potentially exposes us to an IT attack. For an attacker it is very easy to map our profile by following the tracks we leave on social networks, exploiting the vulnerabilities of the tools we use. We must learn to protect information by securing our profiles, sharing our information only with people we know, keeping our systems updated and using reliable security tools. We must be aware that all our actions are tracked on the web, as opposed to those who carry out fraudulent activities on the web. It is therefore an unequal battle where we must avoid being the unaware victims of criminal organizations that have found the way to make money very easily. Ransomware, or viruses with ransom, are a prime example of this. Criminal organizations launch massive attack campaigns on any public account, they hide in countries where computer crimes are not prosecuted, they use virtual currency for their ransoms. The main protective barrier is us, by using these tools with awareness, paying attention to the requests we receive. Only with our help can the attackers enter our systems by opening an executable or accessing a compromised site. We must carefully analyse the messages or emails we receive, and if we are not sure, we must not do what we are asked to do without first verifying its truthfulness."
What is a surprising aspect or passion that your colleagues, or the people who know you, maybe they still don't know about you?
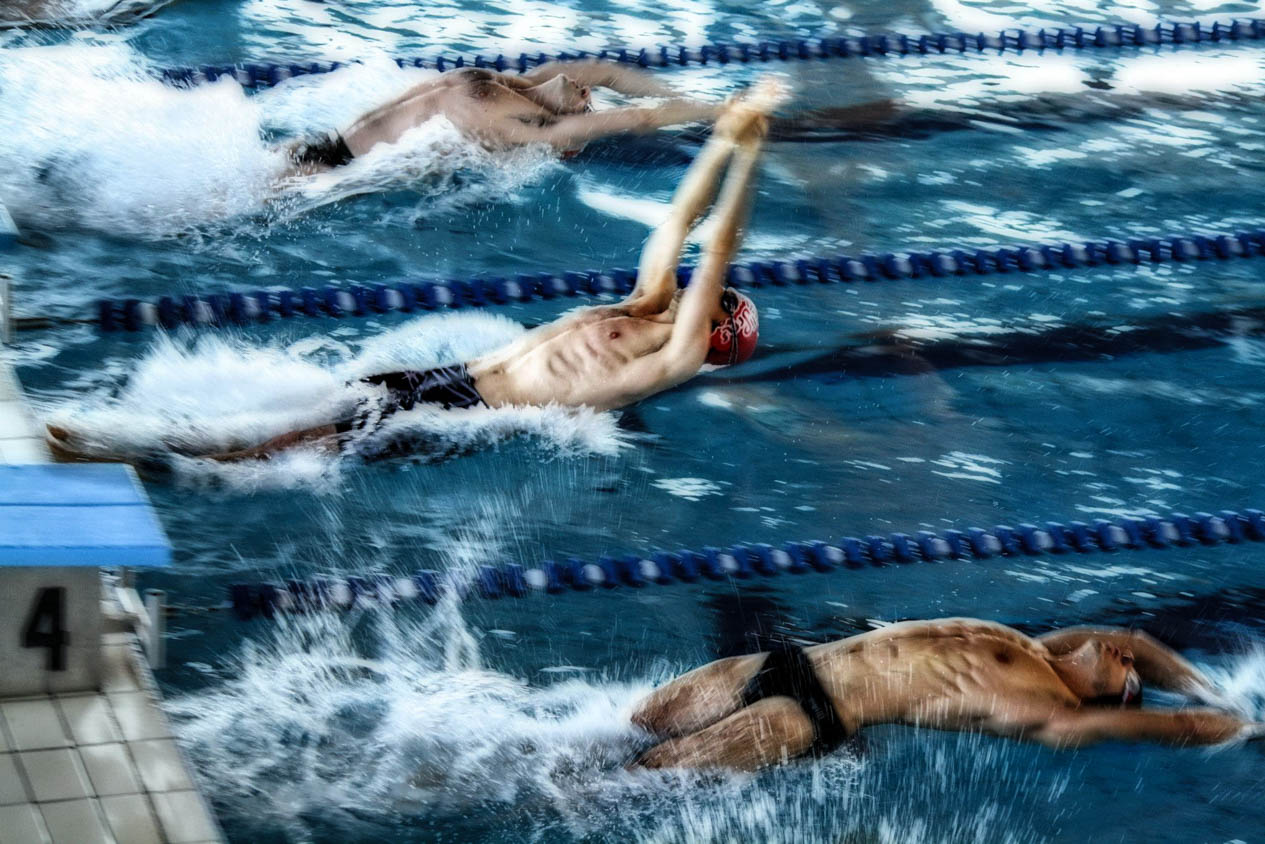
"I think the surprising thing is normality, the satisfaction that comes from the daily small things. Family, friends, sharing one's life with others. But I carve out a small space for myself: my passion for sport, for swimming. Me, the sound of water, the sound of my breath."